Mastering Student Finances with AI: The Ultimate Guide for Comfortable Living
Fri, 28 February 2025

Follow the stories of academics and their research expeditions

Introduction to Cyber Security
Cybersecurity is a fast-growing industry in this era, where the main aim is to reduce cyberattacks. Cybersecurity professionals are responsible for protecting IT infrastructure and controlling devices, networks, and data. So what is cybersecurity? Why is it so important? What are the effective controls used to oppose cyberattacks? Let us learn in detail in this article.
Cybersecurity is a technique that protects internet-connected systems such as computers, servers, mobile devices, and networks from malicious activity. Cyber refers to technology that includes networks, programmes, systems, and data. And security refers to safeguarding all the above-mentioned cyber assets.
Cybersecurity is also called electronic information security or information technology security.
Every organization wants to have an advantage when it comes to securing the systems and information. So the systems should contain strong security features that should keep the organization's data secure.
Therefore, cyber security provides the following domains:
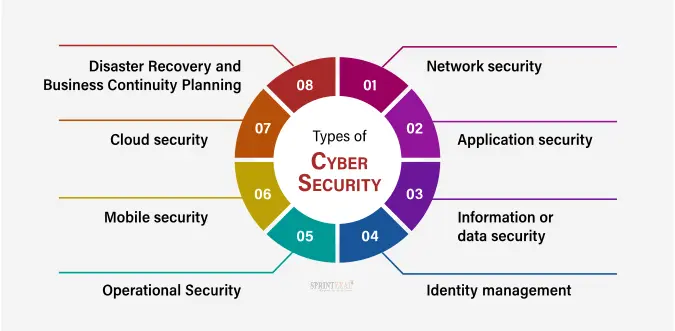
The above-discussed types are essential to bringing cyber security to life.
We live in a digital era where all of our lives revolve around the computer and other electronic devices. All of the critical infrastructures like a banking system, healthcare, financial institutions, governments, and manufacturing industries use internet-connected devices, to perform core operations.
Some of their important information, such as intellectual property, financial data, and personal data, can be sensitive. To protect that data from intruders and threat actors who would want financial gain, cyber security is implemented.
Cyber-attacks have now become an international concern because hacking, and all other security attacks will endanger the global economy. Hence, it is important to have an excellent cyber security strategy, to protect sensitive information from high-profile security breaches.
Governments around the world are paying more attention to cybercrimes. GDPR i.e. General data protection regulation is the best example of how changes are made in cyber security.
Cybersecurity contains essential security goals, which makes it more effective. Let us learn about cyber security goals in the following sections.
The main objective of cyber security is to ensure data protection. Cyber security offers three related principles to protect data from breaches; the principle is called the CIA triad. CIA can be broken into three parts,
- Confidentiality: It gives access to only authorized users, unauthorized users will be blocked. An example of this is Data encryption.
- Integrity: This principle makes sure that the data is authentic, accurate, and safeguarded from unauthorized modification or accidental user modification.
- Availability: Information will be made available only to authorized users. It ensures that malfunctions and cyberattacks are blocked to secure the system.
To secure data from malicious activities Cybersecurity contains essential controls, let us know in the following what it has to offer in detail.
Read more about cyber security and the best protocols used for cyber-attacks.
The controls are created to ensure the CIA triad i.e. confidentiality, integrity, and availability of an organization’s information and technology assets. And controls revolve around four essentials of people, technology, processes, and strategy.
Cyber security control is a mechanism that is used to prevent, detect and reduce cyber-attacks and threats. Cyber security controls are every organization's need, as it is used to manage the security program of a company/organization.
Cyber security is the top priority of organizations, where they determine what control they need. Here are some of the effective smaller controls used by every organization,
Update OS: when a threat or intrusion is found in the software, the technical staff try to work on it and will provide an updated version of the software. Keeping the system updated will help control the threats and security features will get better.
Granted applications: Meaning that a computer is configured to only run an application that is permitted by the organization. This control is hard to manage application in cyber security if done, there will be no cyber-attacks or data breaches taking place.
Reinforce system’s security: Being aware of the programmable settings in the OS i.e. operating system and applications are configured for security. And it is recommended to regularly re-install parts of the OS that will never be used.
Implement Multi-factor authentication: adding two-step verification is going to do good, to keep your data secure. The best example is Gmail, where you can set two-step verification so that no one can get into your mail details.
One of the most widely adopted approaches within multi-factor authentication is SMS OTP Verification, where a one-time password sent to a user’s mobile device adds an extra layer of identity assurance against unauthorized access.
Suggested Read: Get CISM certification and become a certified security manager.
All systems contain weaknesses where some might be simple and some are complex. If a cyber attacker gets to know about the weak points in the system they will try to exploit it. Measures taken by an organization to stop these threats are known as security control.
Cyber security controls are the countermeasures taken up to reduce the chances of a data breach or system attack. The essential and tough work to do in cyber security is to select the right control, but most organizations do it wrong.
Cyber threats are automated and aimed at by cyber attackers. The attacks can be in the forms of malware, formjacking, Cryptojacking, Domain name system attacks, and in various ways they try to get into the system. It becomes a challenge to face all these, cyber security controls help to mitigate most of the threats.
For users on Apple devices, using anti malware for Mac adds an extra layer of defense against such evolving threats. Reducing the threats is always a need, errors that happen in the system can be controlled using essential cyber controls like,
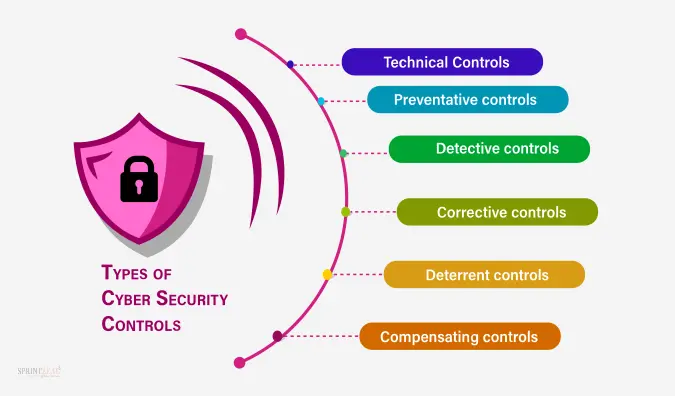
Controls in cyber security contain different classes that split up the types of controls, which are considered based on their importance and classification.
The essential cyber security controls are divided into three types, technical, administrative, and physical. The main goal of implementing security control is preventative, detective, corrective, compensatory, or deterrent. Let us understand each of them in the following,
Technical Controls
Technical controls are also known as logical controls. That is used to reduce attacks on both hardware and software. And automated software tools are installed to protect the system.
In addition to these measures, tools like Multilogin can be employed to manage multiple browser profiles securely.
Examples of technical controls that are used to protect the system are as follows,
Technical control is implemented using two methods,
Access Control Lists (ACL): ACL is a network traffic filter that controls incoming and outgoing traffic. They are commonly used in routers or firewalls, but they can also be programmed in any device that runs on the network, from hosts to servers.
Configuration Rules: It is a set of instructional codes used to guide the execution of the system when information is passed through it.
Administrative controls: Administrative security controls refer to policies, procedures, and guidelines that define the roles or business practices of an organisation’s security goals.
To implement administrative controls, additional security controls are necessary for monitoring and enforcement. The controls used to monitor and enforce them are as follows,
Management controls: This control is used to mainly focus on risk management and information security management.
Operational controls: The security controls that are primarily implemented, like technical and managerial controls executed by people, are saved by operational controls.
Physical controls: Physical security controls in cyber security are implemented based on cyber measures in a defined structure. That is used to detect or prevent unauthorized access to sensitive data.
Examples of physical controls are as follows:
- Closed-circuit surveillance cameras
- PoE camera systems
- Motion or thermal alarm systems
- Security guards and picture IDs
- Locked and dead-bolted steel doors
- Biometrics
Preventative controls
These controls are used to prevent loss or errors. Examples of preventative controls are as follows,
Detective controls
It is an accounting term, that uses internal control to find errors within the organization. Examples of detective controls are as follows:
Corrective controls
After a system malfunction, corrective controls are used to make the system more effective to use. Examples of corrective controls include,
Deterrent controls
Deterrent controls are used to reduce deliberate attacks, which are usually in the form of a tangible object or person. Examples of deterrent controls include
Compensating controls
Compensating control is an alternative method that is used to satisfy the requirement for security. And certain security measures can’t be implemented due to financial or simple impractical reasons at the time.
Example of Compensating control,
Time-based OTP- One of the best examples for compensating control is OTP, i.e., One-time password, where a code is generated by an algorithm that uses the current time of day as one of its authentication factors.

The digital world of today offers many cyber threats to which businesses must defend themselves against from data integrity to financial stability and operational resilience. Cyber Security Controls must be enforced on the digital assets at organization level to mitigate changing risks. Cyber security risks are the most important of the following
Malware Attacks –Viruses, worms and ransomwares are just some of the malware which can infiltrate systems and siphon sensitive data.

To mitigate these risks, organizations must implement strong Cyber Security Controls, which include:
By adopting a proactive approach, organizations can minimize vulnerabilities and strengthen their cyber defense mechanisms.
Assessing Cyber Security Controls is a critical process to ensure the effectiveness of an organization's security framework. A well-structured assessment helps identify weaknesses, improve security posture, and comply with industry regulations.

Key Steps in Cybersecurity Controls Assessment:
1) Identify Assets and Risks
Inventory all digital assets, including hardware, software, and sensitive data.
Conduct a risk assessment to understand potential threats and vulnerabilities.
2) Evaluate Existing Security Measures
Review firewalls, encryption protocols, access controls, and endpoint security solutions.
Analyze log monitoring and security audit reports for anomalies.
3) Compliance and Regulatory Checks
Ensure compliance with GDPR, HIPAA, ISO 27001, and other relevant standards.
Implement security policies that align with industry best practices.
4) Penetration Testing and Vulnerability Scanning
Conduct simulated attacks to test the resilience of security controls.
Use automated tools to scan for vulnerabilities in networks and applications.
5) Employee Awareness and Training
Assess the effectiveness of security awareness programs.
Conduct phishing simulations and cyber hygiene training sessions.
6) Incident Response and Recovery Evaluation
Review the organization's ability to detect, respond to, and recover from cyber incidents.
Update incident response plans based on new threats and lessons learned.
7) Continuous Improvement and Monitoring
Regularly update security policies and controls to address emerging threats.
Leverage threat intelligence and real-time monitoring tools for proactive security management.
By conducting a thorough Cyber Security Controls assessment, organizations can enhance their security infrastructure and ensure continuous protection against cyber threats.
Cyber security is one of the important aspects of the growing world. Threats are hard to deny and overcoming them is also a difficult task. But there is a need to learn how to defend them and also to manage the security activities of organizations and individuals. That could be done by using proper security controls. Monitor the valuable assets and keep your organization away from cyber threats.
Learn more about networking and security with our industry-level all courses and get certified by ISC2 through Sprintzeal. Contact us for further course details or email us, subscribe to our newsletters.
What are controls in cyber security?
Cyber security controls are measures put in place to protect digital systems, networks, and data from cyber threats. These controls help organizations prevent, detect, and respond to security risks effectively. Examples include firewalls, encryption, multi-factor authentication, and security awareness training.
What are the 5 basic security controls?
The five basic security controls that every organization should implement are:
What are the 4 types of security controls?
There are four main types of cyber security controls:

Fri, 28 February 2025

Thu, 20 March 2025

Mon, 21 January 2926

© 2026 Sprintzeal Americas Inc. - All Rights Reserved.